Table of Content
Before you resolve on selecting the hosting service, make sure to look into different options and the packages they provide. If they offer robust and effective security plans and packages, then you should go for their providers. Adding redundancy to the servers is amongst the most applied prevention methods. Adding redundancy to your infrastructure will assist you to maintain the flow of traffic and communication between the end-user and the server without creating any troubles.
In commoditizing DDoS, threat actors made a formidable weapon obtainable to only about everybody by way of marketplaces on the Clearnet and Darknet. The course of turned more efficient such that, whilst slightly fewer assaults succeed, the fee to companies focused continues to rise. Today’s campaigns value companies $22K per minute and more than $200K per assault in 2021 . Malice, greed, and political strain nonetheless high the list of motives driving DDoS attacks.
Permitting And Denying Specific Ips
By successively sending malformed pings, slow pings, and partial packets. The attacking system can set off an overload of reminiscence buffers in the goal. The Accumulate staff has a broad range of innovative instruments to make use of to extend safety and resilience to attacks. Accumulate is devoted to take benefit of safe, performant blockchain for DApps, Enterprise, and your mother and pop. In other words, anchoring is useful as a end result of it minimizes vulnerability to 51% attacks by anchoring to different Layer 1 blockchains.

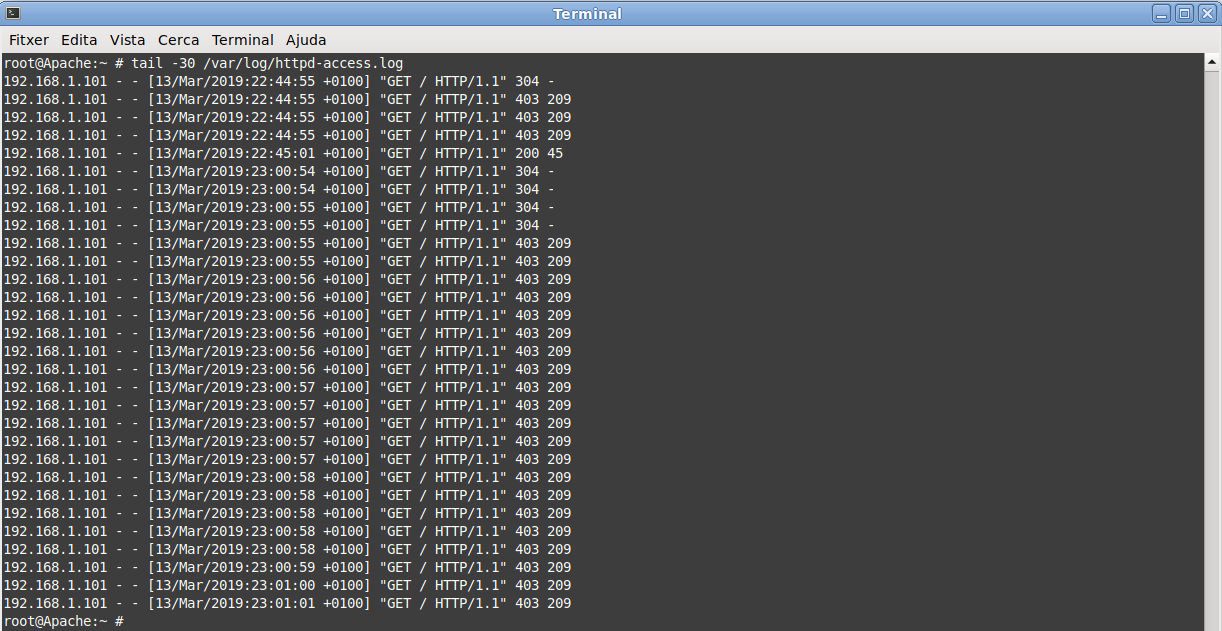
Abstract Dependency on the internet is escalating day-to-day, which makes it vulnerable to myriad security threats, for example phishing, SQL injection, malware and attacks. These threaten a quantity of of the CIA triad components, which are Confidentiality, Integrity and Availability. Hence, ensuring steady safety has turn out to be an inseparable challenge.
High 10 Greatest Printers For Small Businesses To Purchase This 12 Months
To help you with that, I wish to study targeted DDoS API attacks and what they do to your utility programming interfaces, also called API endpoints. The advantage of the cloud-based deployment model is that you don’t have to put in any wearable device. Lastly, the hybrid deployment model provides you the best of both worlds by mixing each approaches collectively.
But they are a must to implement as a result of not implementing these methods will cost you more. Early detection of these attacks will save your servers from crashing and failing to serve the user’s needs. These kinds of attacks must be handled gently and properly in order that the web users aren't affected. Without preventing these assaults, there is no method you'll be able to enhance your web site performance and consumer expertise. If these assaults usually are not dealt with nicely, they could end in large losses for many web site homeowners and organizations.
Review Existing Rate-based Rules And Think About Decreasing The Rate Limit Threshold To Block Unhealthy Requests
Add filters that block packets from apparent attackers (junk or blacklisted IP addresses, infected gadgets, etc.). If you haven’t arrange DDoS safety for VPS or your dedicated server, there’s little you are able to do throughout an actual assault. However, there are some preventative measures you'll find a way to take to stop the lowest stage of DDoS from going down.
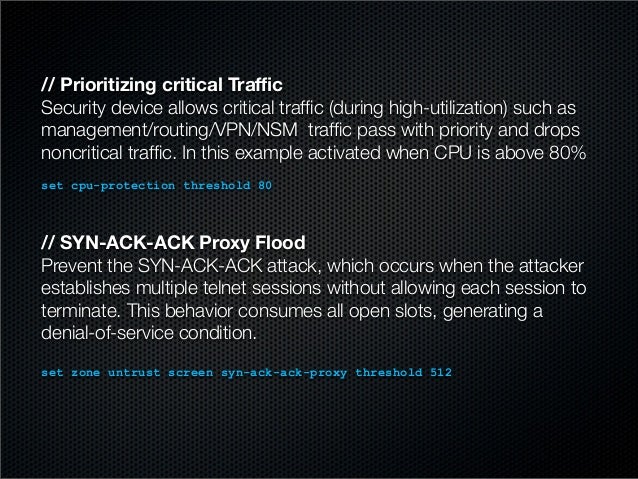
We wish to be certain that we do not expose our purposes or assets to ports, protocols, or applications that aren't anticipating any communication from them. As a result, the potential factors of assault are lowered, permitting us to focus our mitigation efforts. In different cases, firewalls or Access Control Lists can be used to control what traffic reaches your applications. A Distributed Denial of Service is a targeted cyber assault on a website or gadget where a malicious attacker's flood of visitors is shipped from single or multiple sources.
By monitoring these tendencies, if there is an unusual push of visitors, will probably be straightforward to establish and mitigate. Having full visibility of your network and what’s on your community will hold it secure and less vulnerable to assaults exploiting vulnerabilities. Determining and documenting volumes will assist mitigate an assault before it takes down your network or earlier than an finish user even is conscious of anything has occurred. As a solution provider, preparing and protecting companies from cyber threats is something CCI Systems does each week. Despite the low barrier of entry, a DDoS attack of this size lacks scale, and it'll not be strong enough to take down a larger goal, like a service supplier or operator. DDoS attacks may be classified primarily based on which layer of the Open Systems Interconnection mannequin they target.
Even if they occur, you must have some defined methods and strategies to mitigate these attacks. You also can seek the help of hosting specialists that offer numerous safety plans to fight such assaults. Such effective plans have to be included in your web hosting, and your choice of the net host is determined by the packages supplied. You must remember that when you opt for cheaper hosting providers, then there isn't any assure that you may be protected from any attacks. If you need safe communications with end-users with none problems, then a safe host is the only choice.
Russian Hackers Use Western Networks To Attack Ukraine
The deployment mannequin you select should rely in your threat profile, kind of attacks, and on-premise installation. In an on-premise deployment model, a device is installed which analyzes visitors earlier than reaching your network. This could be a nice choice if you wish to safeguard in opposition to low and slow attacks.

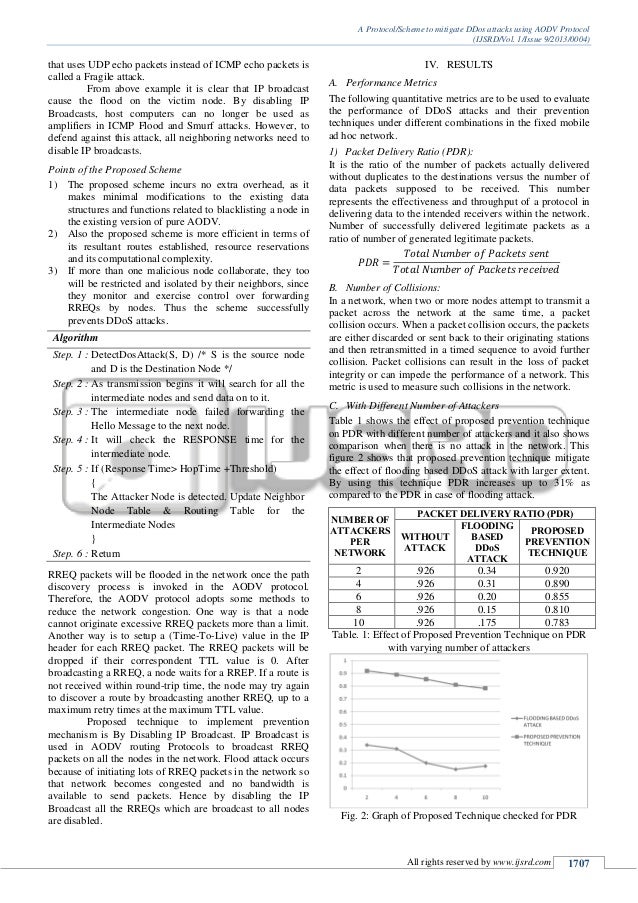
Now, we’ll see how you can benefit from a content supply community with a honeypot. First we set up the apache server and hosted a easy website and requested it from an excellent few customers. We captured this traffic and analyzed it using wireshark , which is a network protocol analyzer that captures community packets and tries to display that packet knowledge as detailed as attainable.
DoS assault specifically is an assault by hackers wherein they use a pc or a set of computer systems to flood a server with TCP and UDP packets thus stopping customers to haven't any access to their service. These kinds of safety attacks in your community and servers at all times have an result on the performance of your website. For a better and effectively performing website, the server and the community should be freed from attacks and vulnerabilities. For guaranteeing a website’s efficiency, make certain the host hosting your web site has higher and dependable security plans and packages. One of the main methods to avoid these assaults is by implementing a powerful and efficient response plan. You must have a powerful strategy and plan carried out to keep away from such attacks from happening.
Q2 2019, according to the most recent figures from the Russian AV vendor3. A rise in multi-vector DDoS attacks has brought on visitors congestion by flooding networks with quite a few illegitimate network packets.5. In April 2019, a DDOS assault was hit by one of the shoppers of Imperva with 580 million packets per second.
Simple Methods To Mitigate Dns Primarily Based Ddos Assaults
Using a Web Application Firewall to guard towards assaults such as SQL injection or cross-site request forgery that try to exploit a vulnerability in your utility is an efficient apply. It can also help mitigate assaults because they've skilled assist to study visitors patterns and create customized protections. When we detect excessive traffic levels hitting a number, our baseline is to simply accept solely as much visitors as our host can handle without affecting availability. More superior safety techniques can go a step further and intelligently settle for solely reliable site visitors by analyzing individual packets. To achieve this, you have to first perceive the traits of excellent site visitors that the goal usually receives and then examine each packet to this baseline.

No comments:
Post a Comment